| If you have a Google account — and who doesn’t? — you may have discovered that there are various ways to upload photos to that account. You also may have noticed that there seem to be two different places where your photos can be stored: Google Photos and Google Drive. This post explains the basics of how each of these work and how you might use them to backup and work with your photos. | DISCLAIMER: Google has made many changes over the years and will continue to do so. This post describes how things work as of March 2022. As time goes by, things may no longer work as described here. |
How They Work
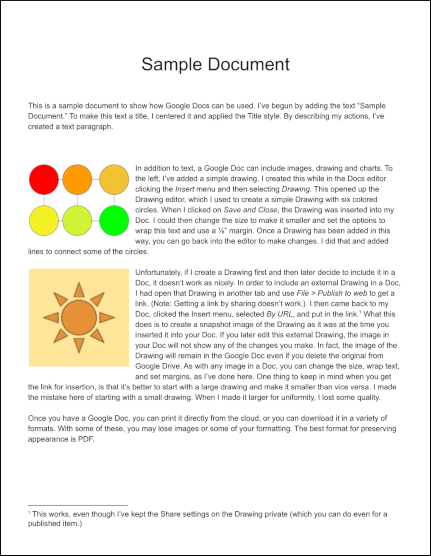
Google Photos and Google Drive both let you upload photos to your account’s cloud storage, but their purpose is different. If you think of your cloud storage as being similar to a hard drive on a computer, Google Drive is like a file manager that allows you to see all your files, including photos, and organize them into folders. You can think Google Photos, on the other hand, as an application that not only stores your photos, but also lets you edit them and organize them for viewing in various ways. Depending on your needs, you can use either or both as cloud storage for your digital photos.
Data Limits
The free storage Google provides for photos and other information is generous, but not unlimited. Prior to June 1, 2021, Google did provide unlimited storage for photos 16 megapixels or less and videos 1080p or less. Such photos and videos uploaded prior to the June 1 date are not counted towards the 15G limit, but photos and videos uploaded after that date are. So when uploading to Google Drive or Google Photos, keep in mind that anything stored in these accounts, along with your stored Gmail messages, counts towards the 15G data limit.
Which to Use?
Advantages of Google Drive
Google Drive might be the right choice, if you just want to have a backup copy of photos in cloud storage to keep them safe. This is especially true if you already have your photos organized in a set of folders that also contain files such as text notes about your photos or files created by photo-editing software such as Photoshop. You can use Google Drive to upload an entire folder structure (subject to some size limits) with subfolders and files of various types. Your folder structure will be preserved and, for backup purposes, you can upload any type of file to Google Drive. This would allow you to have a backup that keeps photos and other related files (including thumbnails and metadata). In addition, Google Drive supports previewing for a variety of file types (.e.g txt, docx, pdf, psd). If, for example, you have txt files with notes, you can use Google Drive to look at those notes as well as your photos. If you later want to download the folder structure you’ve uploaded, Google drive will package your content into an efficient zip file (or multiple zip files for large amounts of data). The files and folders you extract from this will be identical to the originals you used for uploading.
Advantages of Google Photos
Google Photos might be the right choice if, in addition to backup storage, you want some tools for basic editing and organization of your photos. These are not as sophisticated or flexible as those you might find in a computer-based application or in a cloud photo service such as Flickr, but they provide some quick and easy ways organize, search, share and improve the appearance of photos.
Google also provides keyword searching with image recognition capability. This means you can find photos based on the nature of the photo itself, even if you have not give the photo a name or description that matches the keyword. In addition to terms like “birthday” and “flower,” the Google found a nice set of matching photos for “rock,” “ocean,” “bike,” “blue,”and “plaid.” It also correctly recognized that my collection contained no photos with elephants, though a search for “hat” missed party hats, military hats, women’s hats, and many instances of traditional men’s hats.
Strategies for Uploading
Uploading via Browser
Once you are logged into your Google account in a browser, you can upload photos either from the Google Drive (drive.google.com) or from Google Photos (photos.google.com). The main difference between the two is that you can upload either files or folders (which can include subfolders as well as files) to Google Drive, but you can upload only files to Google Photos. Another difference is that you can copy photos from Google Drive to Google Photos — a process Google refers to as “uploading from Google Drive”– but the process does not work in reverse.
One Copy or Two?
If you upload photos to Google Drive and then copy them to Google Photos as described above, keep in mind that each copy will count separately against the 15G data limit. This was not always the case, so if you used the tools Google provided to sync photos in the past, you might want to read the article that appeared in Google’s blog about Changing how Google Drive and Google Photos work together.
Uploading via App
An alternative to uploading via browser is to use an app that will automatically upload photos you put in specified locations to Google Drive or Google Photos. If you are using a Windows or Mac computer, there is a single app you can use, as is explained in the Google support pages on Back up photos & videos and Use Google Drive for desktop. If you a phone or tablet running Android or iOS, there are separate apps for Google Drive and Google Photos, and these usually can be found in the relevant app store for your device, but may not be available or fully functional on some devices (e.g. Amazon Fire tablets).
the app to use is Google Drive for Desktop, which can be set up to upload to Google . You can find information about how to use both methods on the official Google support page: Upload files and folders to Google Drive.
Uploaded vs. Original Files
Sometimes people find it so convenient to use Google Photos that they delete or lose track of the original image files. There are, however, some reasons why you should hang onto your original image files.
By default, Google Photos uses compression to reduce the storage space required for uploaded photos. The compression techniques are good, so you probably won’t see any difference on the screen of your computer, tablet or phone. However, you are likely to get better results with the original uncompressed image if you want to do things like enlarge and crop. Since you can’t always predict future uses for your photos, keeping the original files preserves details that might someday be useful or important.
After uploading photos, you may make changes with Google Photos editing tools. If you later download those photos, depending on the method you use, you may be given a choice between downloading the “original” version or the “edited” version. The “original” version in this case does not mean original quality, but rather means the photo as stored in Google Photos (i.e. perhaps compressed) before you did your editing. Also keep in mind that, while you can undo and redo edits in Google Photos, you cannot do this with edited photos that have been downloaded.
Multiple Backups for Important Photos
Ideally, for photos you value, you will keep three exact copies of your original image files: two on separate media locally and a third in a separate backup location. For example, you might copy your photo files to SD cards or an external hard drive for local backup. For offsite backup, there are a variety of cloud storage service you can use, including Google Drive. You also can change the settings on Google Photos to upload with original quality — but be careful about how you deal with images you have edited with Google Photos.
Additional Information
For additional information, check out Google Photos Help and Google Drive Help.